Technical measures
Understanding GDPR

Shalini Kurapati, CIPP/E
Co-founder and CEO, Clearbox AI
What are they?
- Securing physical and digital spaces
- Data minimization and privacy preservation
- Physical security
- Cyber security
- Information security
- Encryption and Pseudonymization
Physical security

- Access restriction to your work spaces
- Round-the-clock security for data centers
- Other measures include: Locks, alarms
Cybersecurity

- Network, data security, online security, and device security
- Stress tests, secure storage with access controls, anti-malware, and device security controls
- Other technical measures depend on the data processing scale and risks
1 Records management and security guidance, Information Commissioner's Office
Encryption
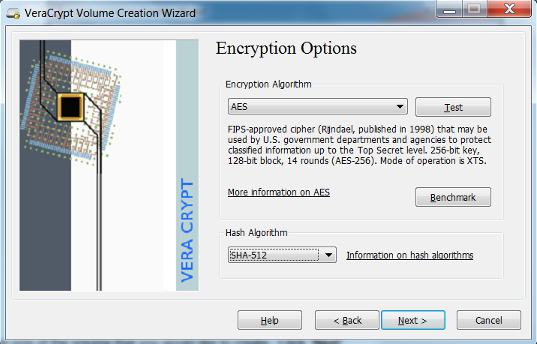
- Encoding data- only intended users
- Effective, low cost
- Many commercial solutions
- Open source and multi platform - VeraCrypt
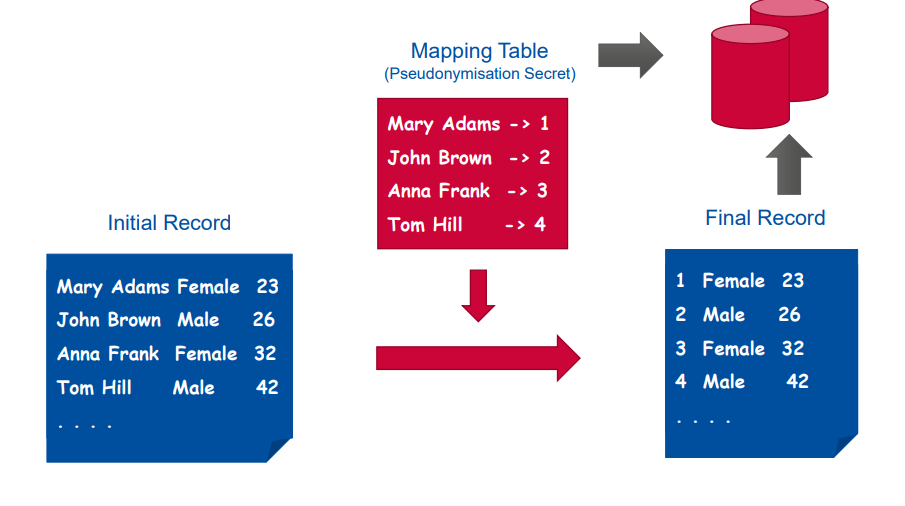
Pseudonymization
- Remove direct identifier, data cannot be attributed to a specific individual
- Counter, random number generator
- Risk mitigation,not anonymization
1 Dr.Prokopios DROGKARIS, European Union Agency for Cybersecurity (ENISA), On overview of existing pseudonymisation techniques, IPEN Webinar 2021
Let's practice!
Understanding GDPR