Security with GitHub Copilot
Software Development with GitHub Copilot

Thalia Barrera
AI Engineering Curriculum Manager, DataCamp
When bugs become vulnerabilities
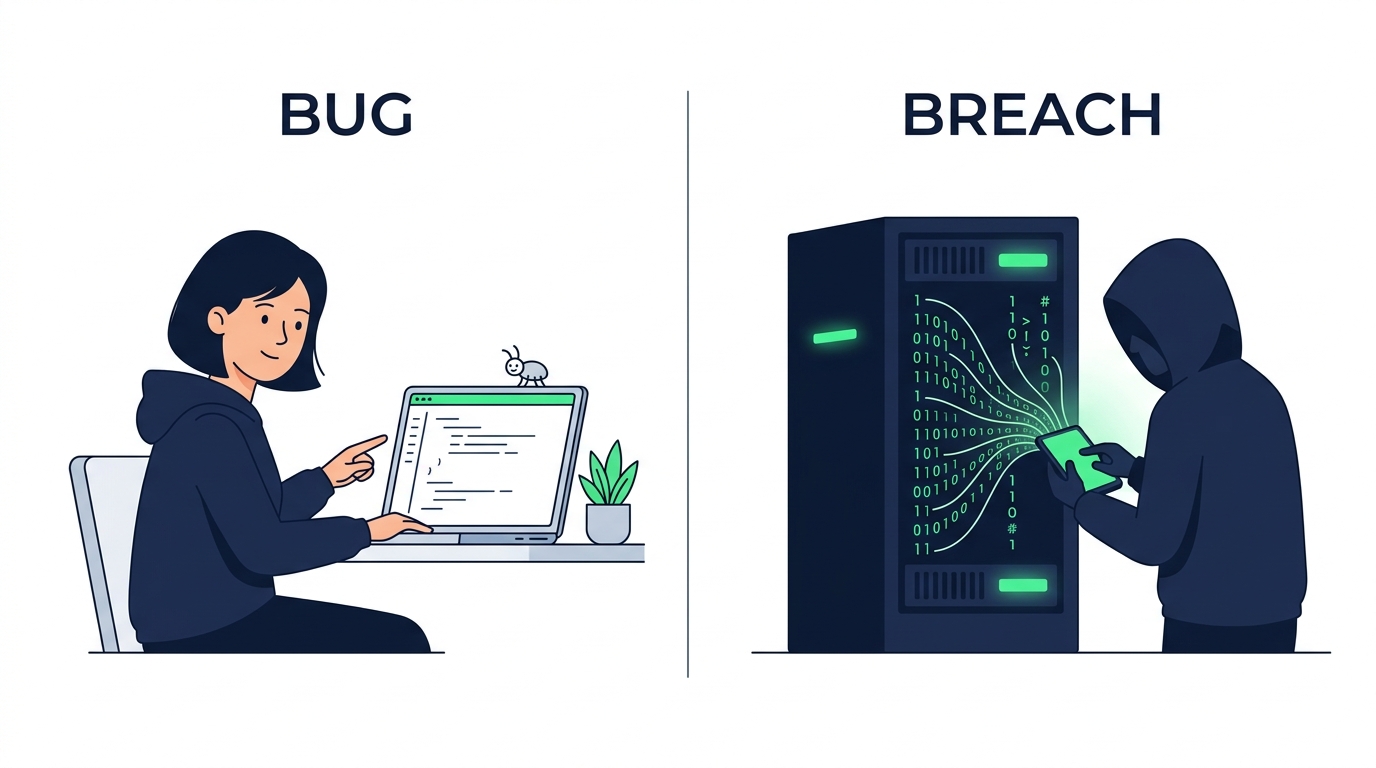
- Vulnerable code often looks identical to other code
- Passes tests, reviews, and sometimes ships to production
- 🤖 Copilot can act as a security reviewer
A vulnerable function
def get_user(username):
query = f"SELECT * FROM users \
WHERE username = '{username}'"
return db.execute(query)
An attacker can inject SQL:
- Bypass authentication entirely
- Dump the whole
userstable - Delete your database
[screencast]
[screencast]
Security prompts that work
Targeted review
Review
#selectionfor SQL injection and XSS vulnerabilities
Codebase-wide scan
@workspacescan for hardcoded credentials or API keys
[screencast]
From review to prevention

Defensive code generation
Add input validation to this endpoint. Reject unexpected types and enforce length limits.
Don't just find vulnerabilities — prevent them
Bake security into every suggestion
.github/copilot-instructions.md
## Security standards
- Use parameterized queries
- Never hardcode credentials or API keys
- Validate and sanitize all user input
- Use bcrypt or argon2 for password hashing
Language-specific security rules
.github/instructions/security.instructions.md
applyTo: "**/*.py"
- Use secrets module instead of random for tokens
- Escape all user input in Jinja2 templates
✅ Security becomes part of how you write code
Let's practice!
Software Development with GitHub Copilot

