AWS Secrets Manager and Parameter Store
Using Data Stores in AWS

Dunieski Otano
AWS Solutions Architect
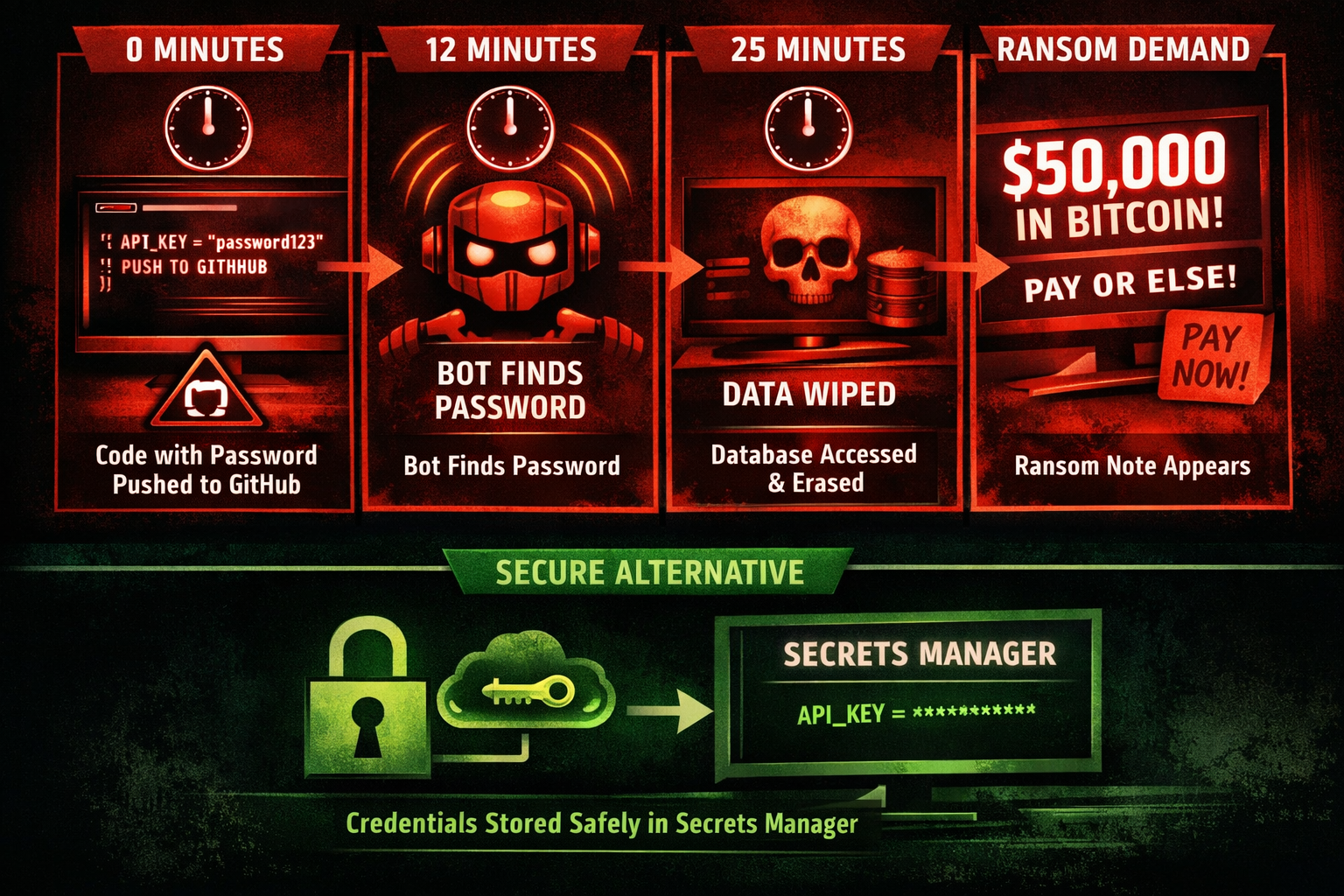
The hardcoded password disaster
- Developer hardcodes database password in code
- Code pushed to public GitHub repository
- Attacker finds password in 12 minutes
- Database wiped, ransom demanded
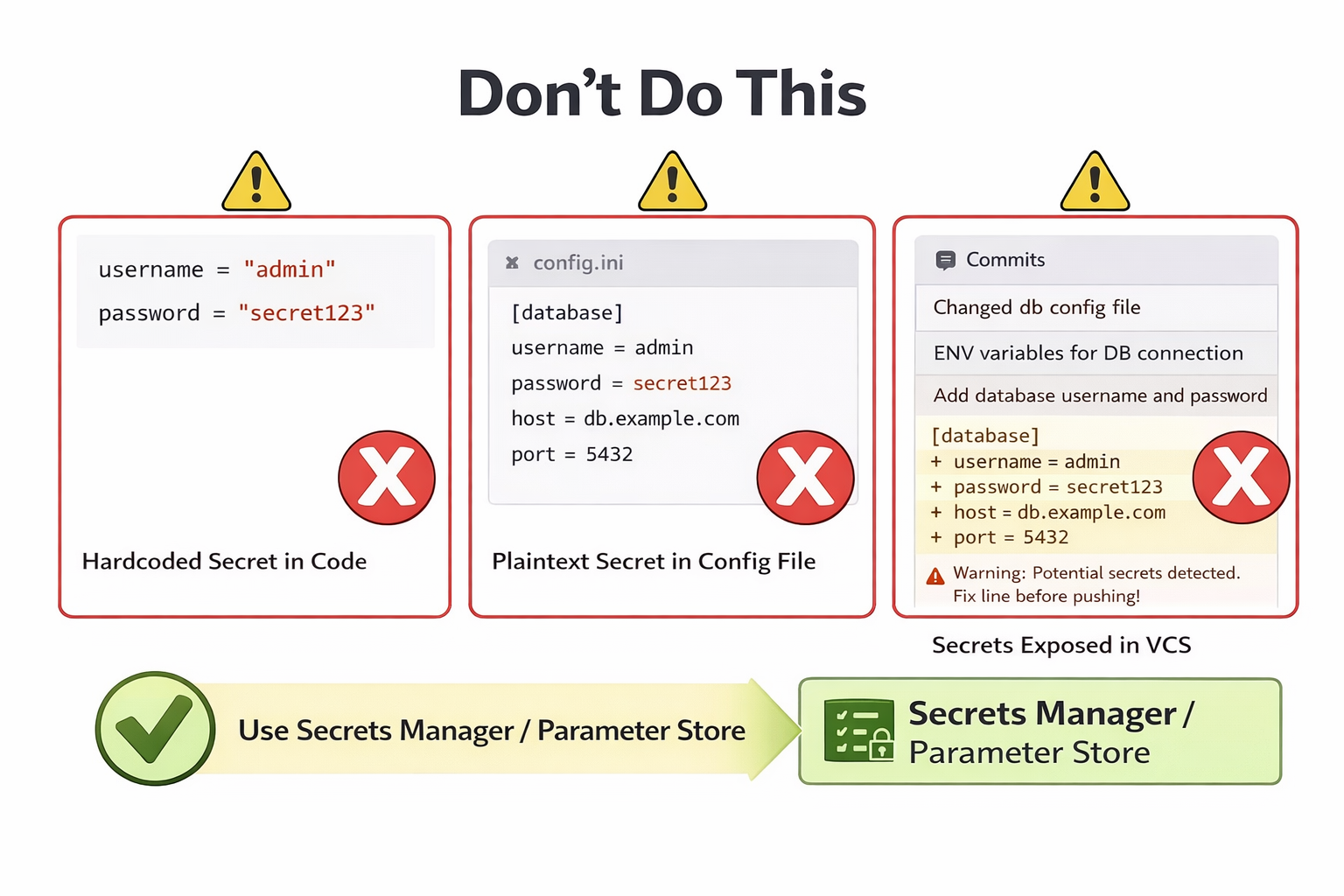
Why never hardcode secrets
- Common mistakes
- Hardcoded in source code
- Plain text in config files
- Committed to version control
- Consequences
- Exposed in public repositories
- Difficult to rotate
- Audit trail missing
AWS Secrets Manager overview
- Purpose
- Store and rotate credentials automatically
- What to store
- Database passwords, API keys, OAuth tokens
- Key features
- Automatic rotation, KMS encryption, audit logging

Secrets Manager automatic rotation
- Rotation process
- Lambda function updates credentials
- Rotation window
- Set when rotation occurs (rate or cron)
- Zero downtime
- Both old and new passwords work during rotation

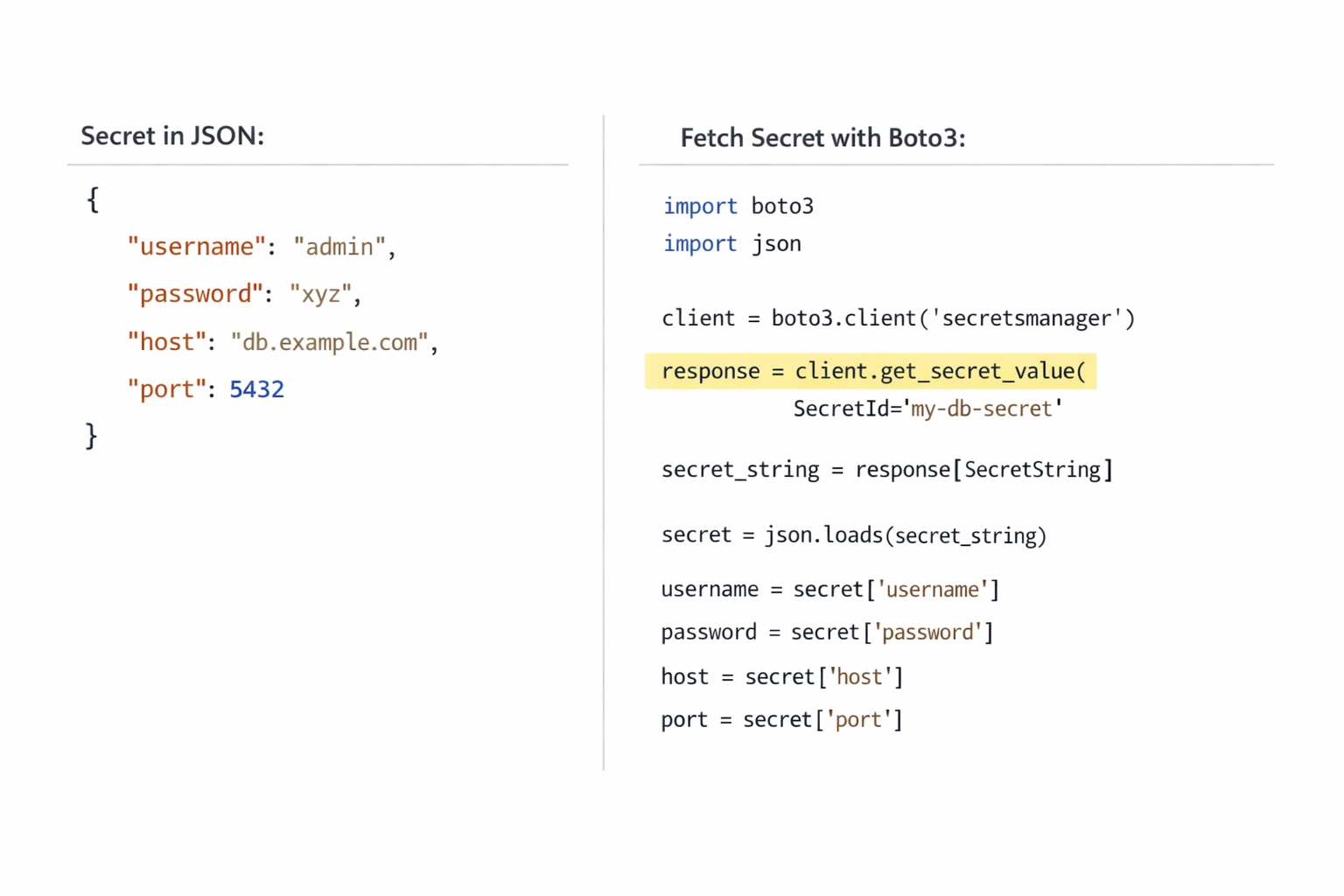
Storing secrets in JSON format
- Structured secrets
- Store multiple values in one secret
- JSON format
- {"username": "admin", "password": "...", "host": "db.example.com"}
- Retrieve and parse
- Use GetSecretValue API
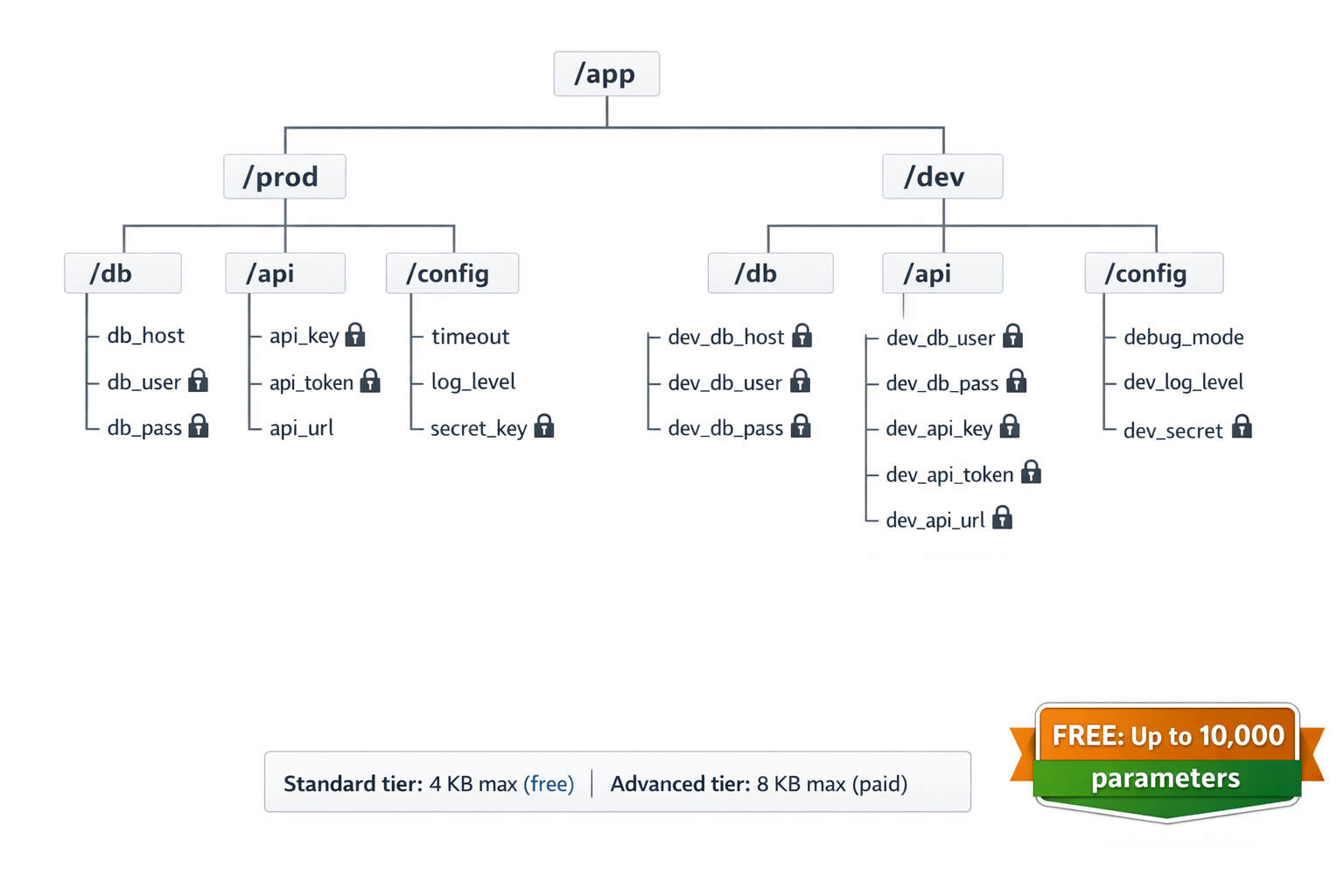
Parameter Store overview
- Part of AWS Systems Manager
- Purpose
- Store configuration and static secrets
- Hierarchical organization
- /app/prod/db/password
- /app/dev/api-key
- Free tier
- Up to 10,000 standard parameters (4 KB max)
- Advanced parameters (8 KB max) incur costs
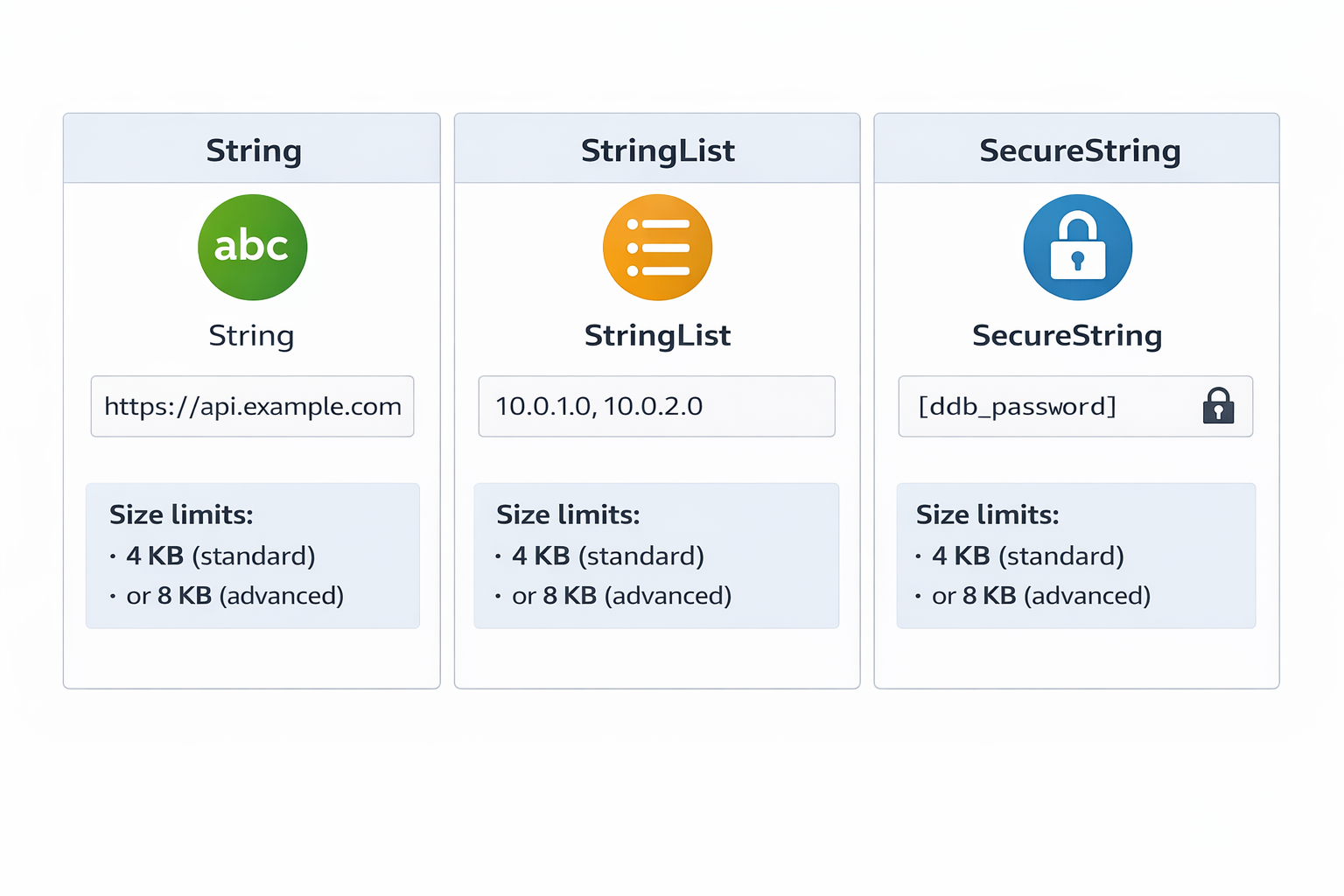
Parameter Store parameter types
- String
- Plain text configuration (feature flags, endpoints)
- StringList
- Comma-separated values (IP addresses)
- SecureString
- Encrypted with KMS (passwords, API keys)
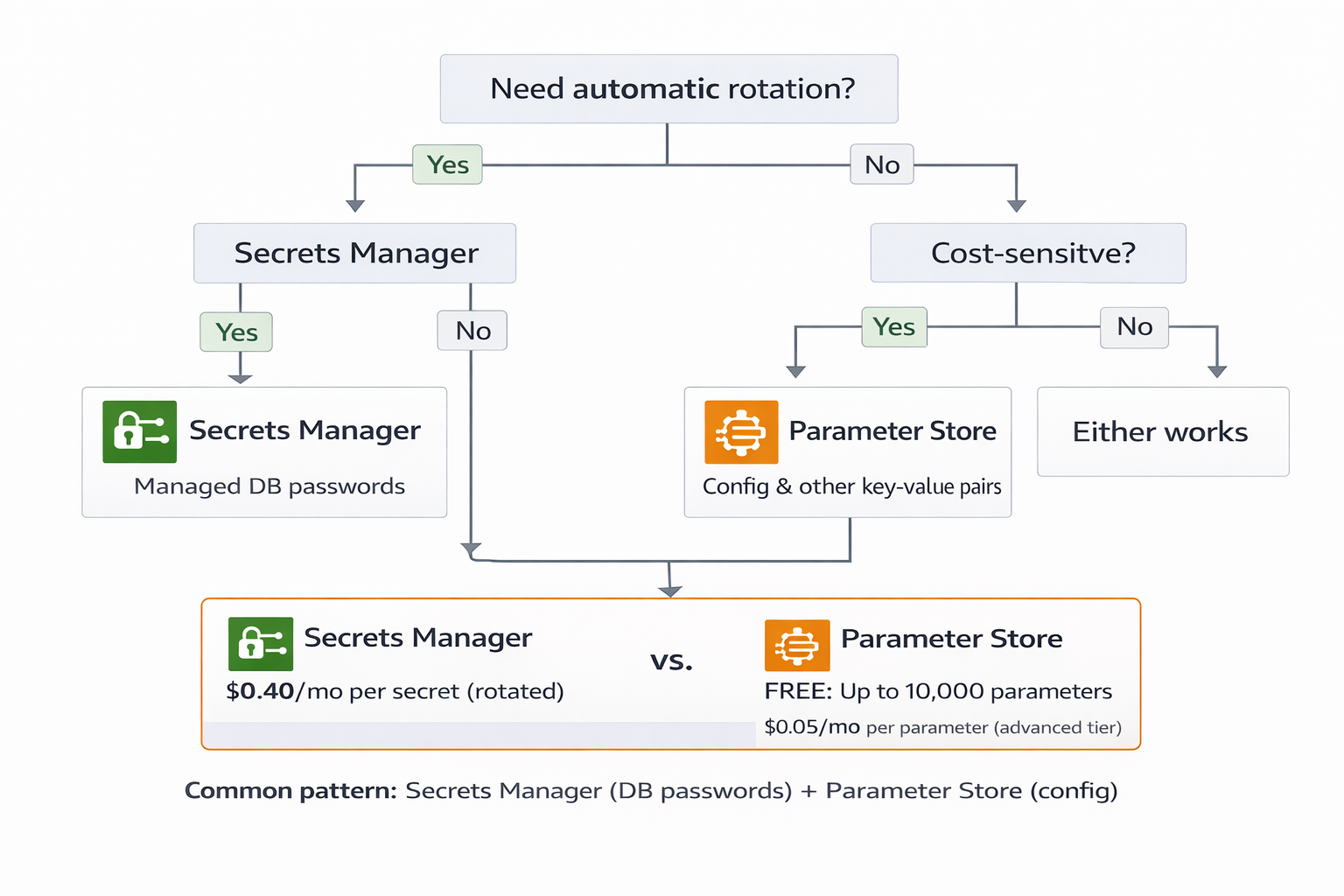
Secrets Manager vs Parameter Store decision guide
- Use Secrets Manager when
- Need automatic rotation
- Storing database credentials
- Use Parameter Store when
- Static configuration values
- Cost-sensitive (free tier)
- Use both together
- Common pattern in production
Let's practice!
Using Data Stores in AWS

