Data classification, encryption, and AWS KMS
Using Data Stores in AWS

Dunieski Otano
AWS Solutions Architect
The data breach that could have been prevented
- Healthcare company stores patient records in DynamoDB
- No encryption enabled
- Data breach exposes 2 million patient records
- HIPAA violation: $50 million fine

Understanding data classification
- Why classify data?
- Apply appropriate security controls
- Meet compliance requirements
- Classification levels
- Public, Internal, Confidential, Restricted
- Impact of misclassification
- Regulatory fines, data breaches

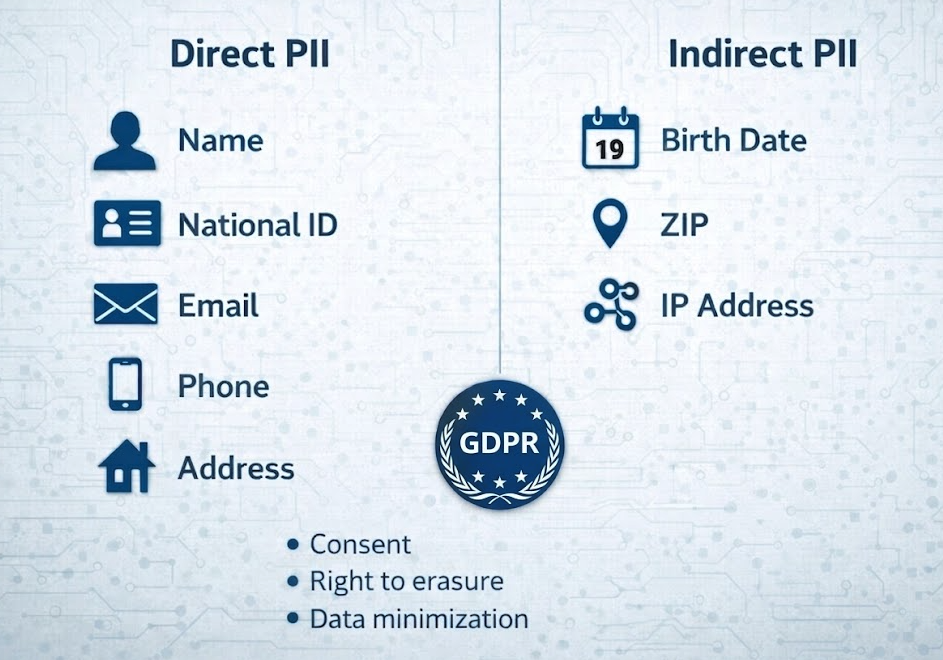
PII: Personally Identifiable Information
- Direct identifiers
- Name, national ID, email, phone, address
- Indirect identifiers
- Birth date, ZIP code, IP address
- GDPR requirements
- Consent, right to erasure, data minimization
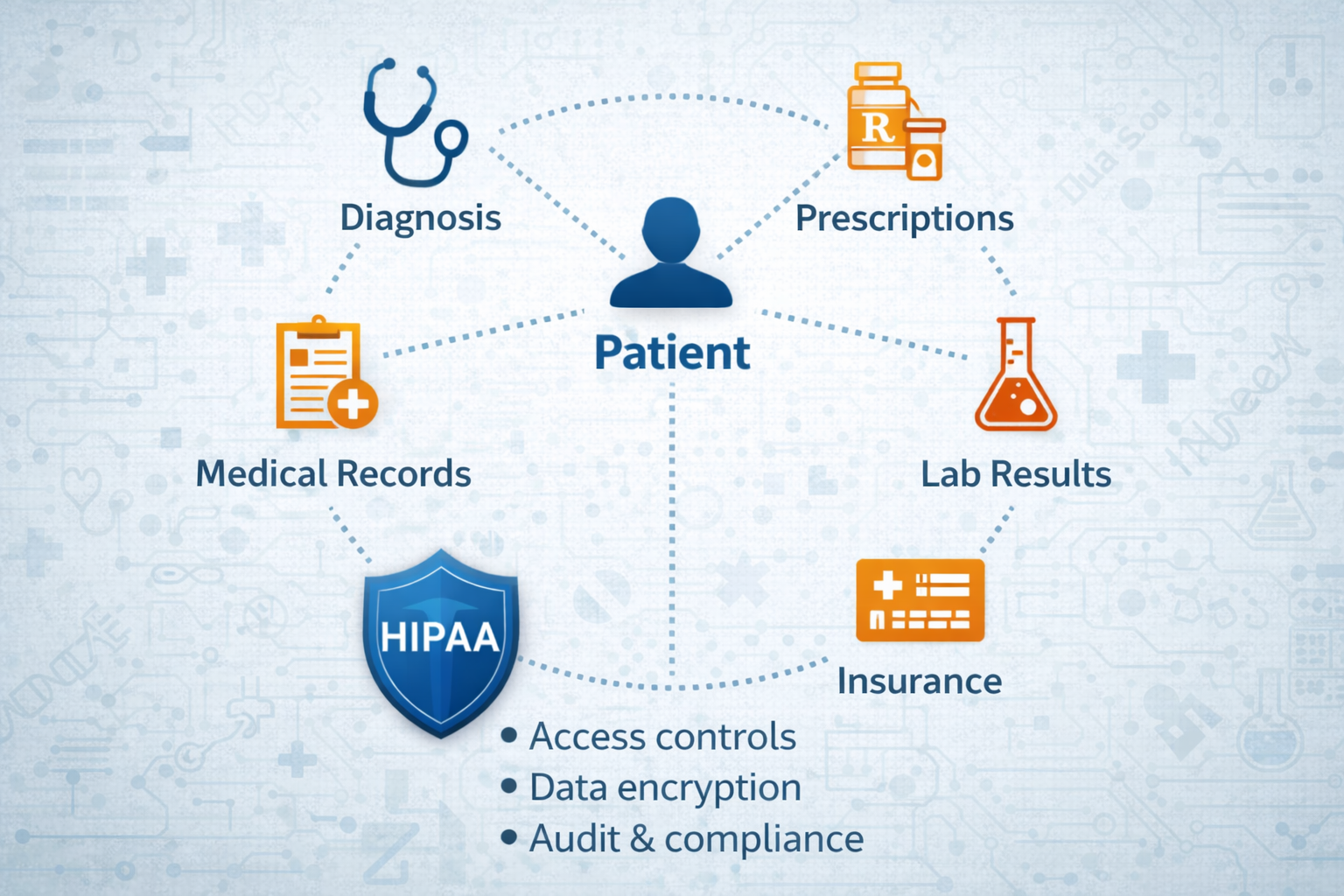
PHI: Protected Health Information
- Medical information
- Diagnoses, treatments, prescriptions, lab results
- Health identifiers
- Medical record numbers, insurance IDs
- HIPAA requirements
- Encryption, access controls, audit logs
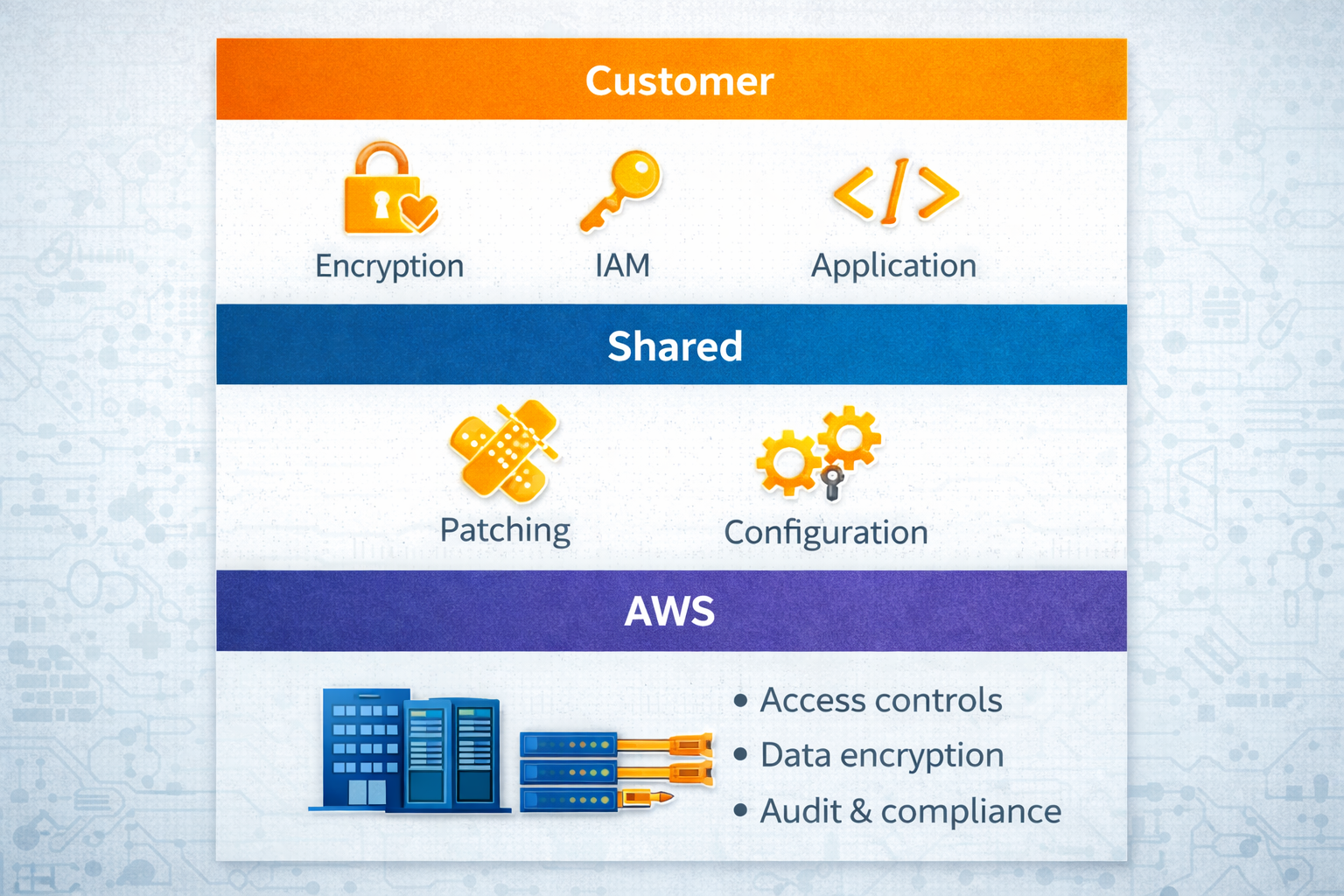
AWS Shared Responsibility Model
- AWS secures the cloud
- Physical security, hardware, network
- You secure IN the cloud
- Data encryption, IAM policies, application code
- Shared controls
- Patch management, configuration
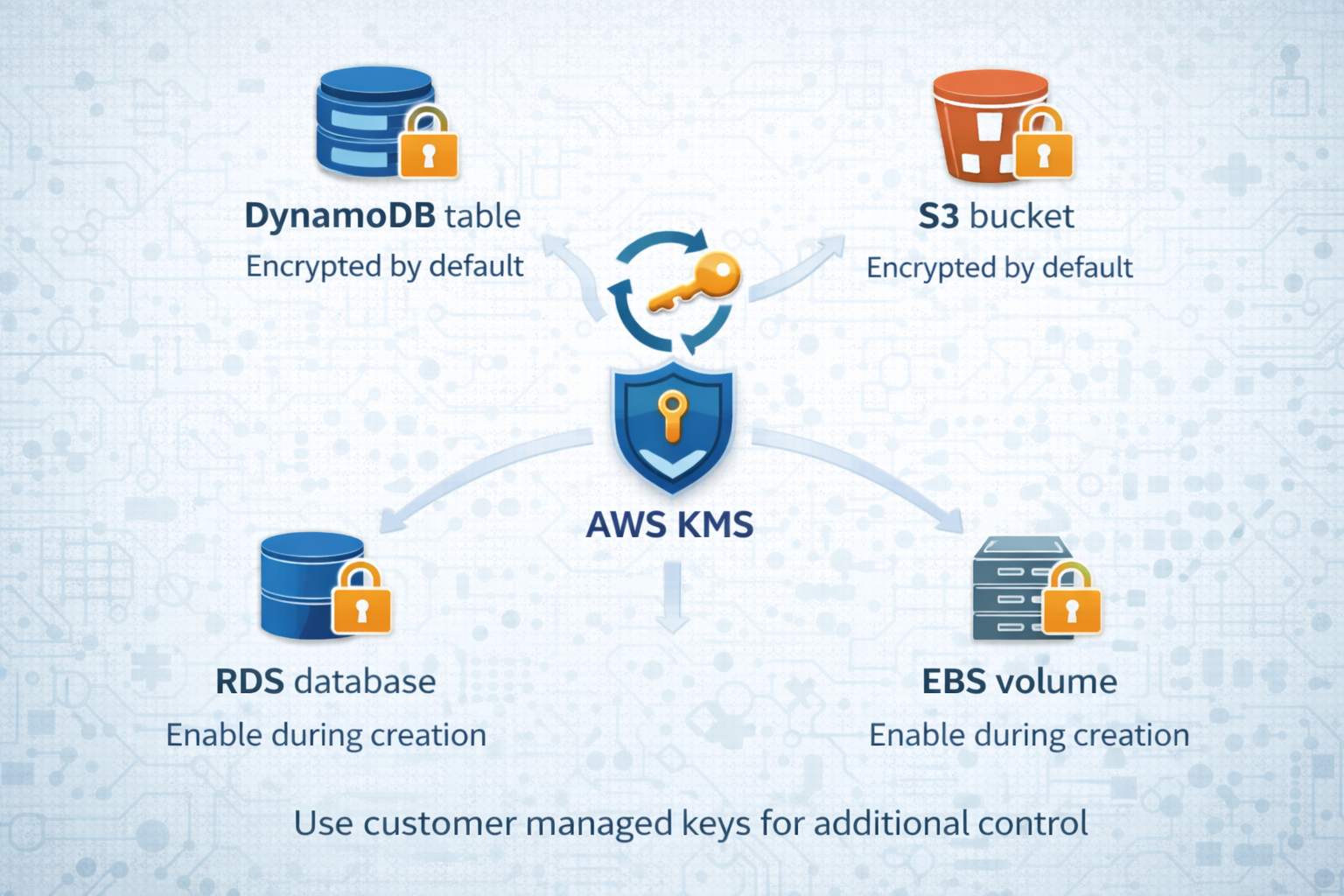
Encryption at rest with AWS KMS
- What is encryption at rest?
- Protects data stored on disk
- AWS KMS
- Centralized key management
- Automatic key rotation
- Enable in services
- DynamoDB, S3, RDS, EBS
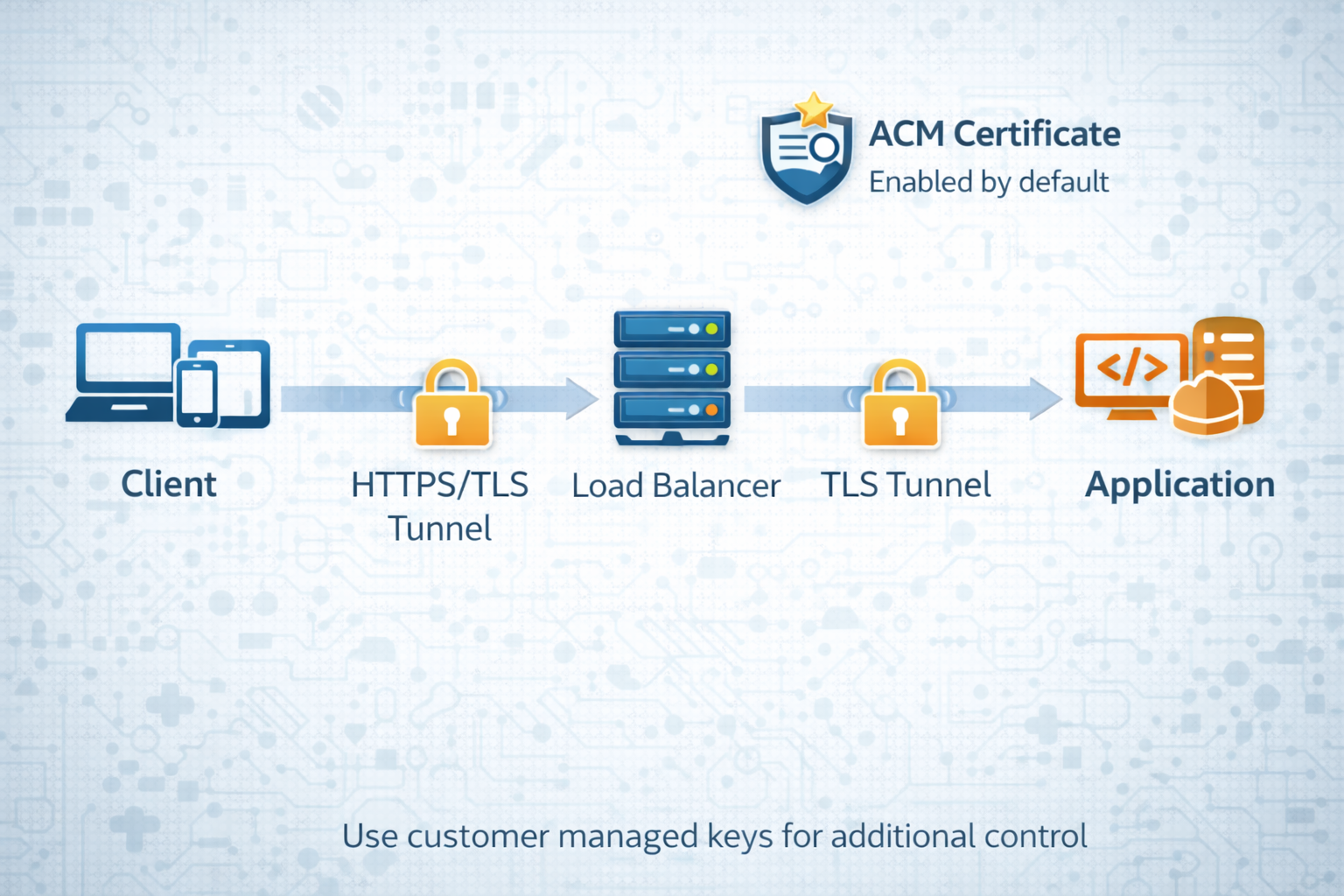
Encryption in transit with TLS
- What is encryption in transit?
- Protects data moving over network
- TLS/HTTPS
- Industry standard protocol
- Enabled by default in AWS
- Certificate management
- AWS Certificate Manager (ACM)
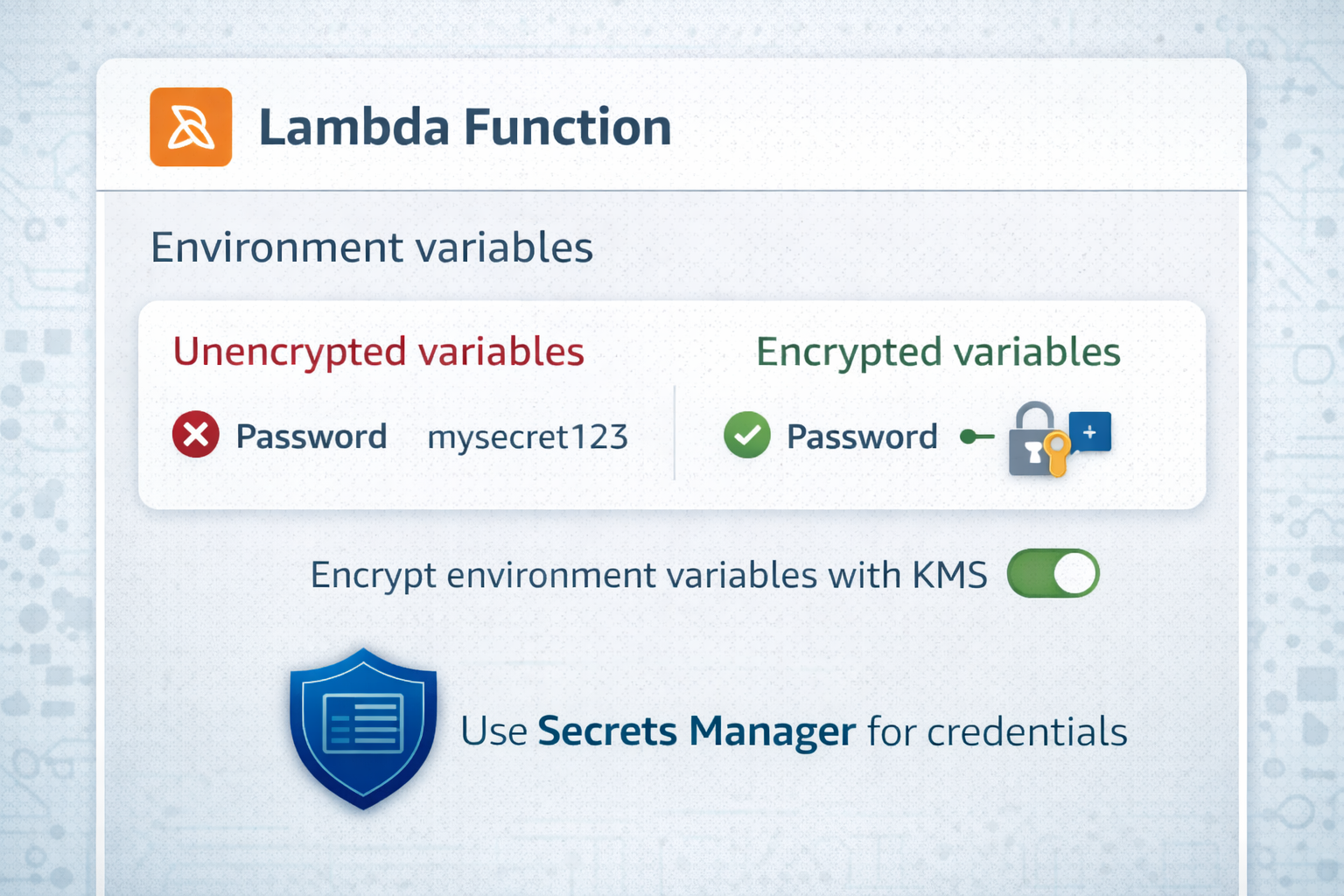
Encrypting Lambda environment variables
- Environment variables
- Store configuration in Lambda
- Encryption at rest
- Select KMS key when creating function
- Encryption helpers
- Encrypt in transit from console to Lambda
- Secrets Manager: AWS Security Best Practices
Let's practice!
Using Data Stores in AWS

