Security-first development with AI
Advanced AI-Assisted Coding for Developers

Thalia Barrera
AI Engineering Curriculum Manager, DataCamp
From testing to security

- Well-tested doesn't mean safe
- Focus on preventing vulnerabilities before they reach production
Security-first principles
- ✔ Find vulnerability patterns early
- ✔ Fix with secure practices, not patches
- ✔ Automate security checks
Why AI for security?

- Scan unfamiliar code quickly
- Surface risky hotspots
- Propose concrete remediations
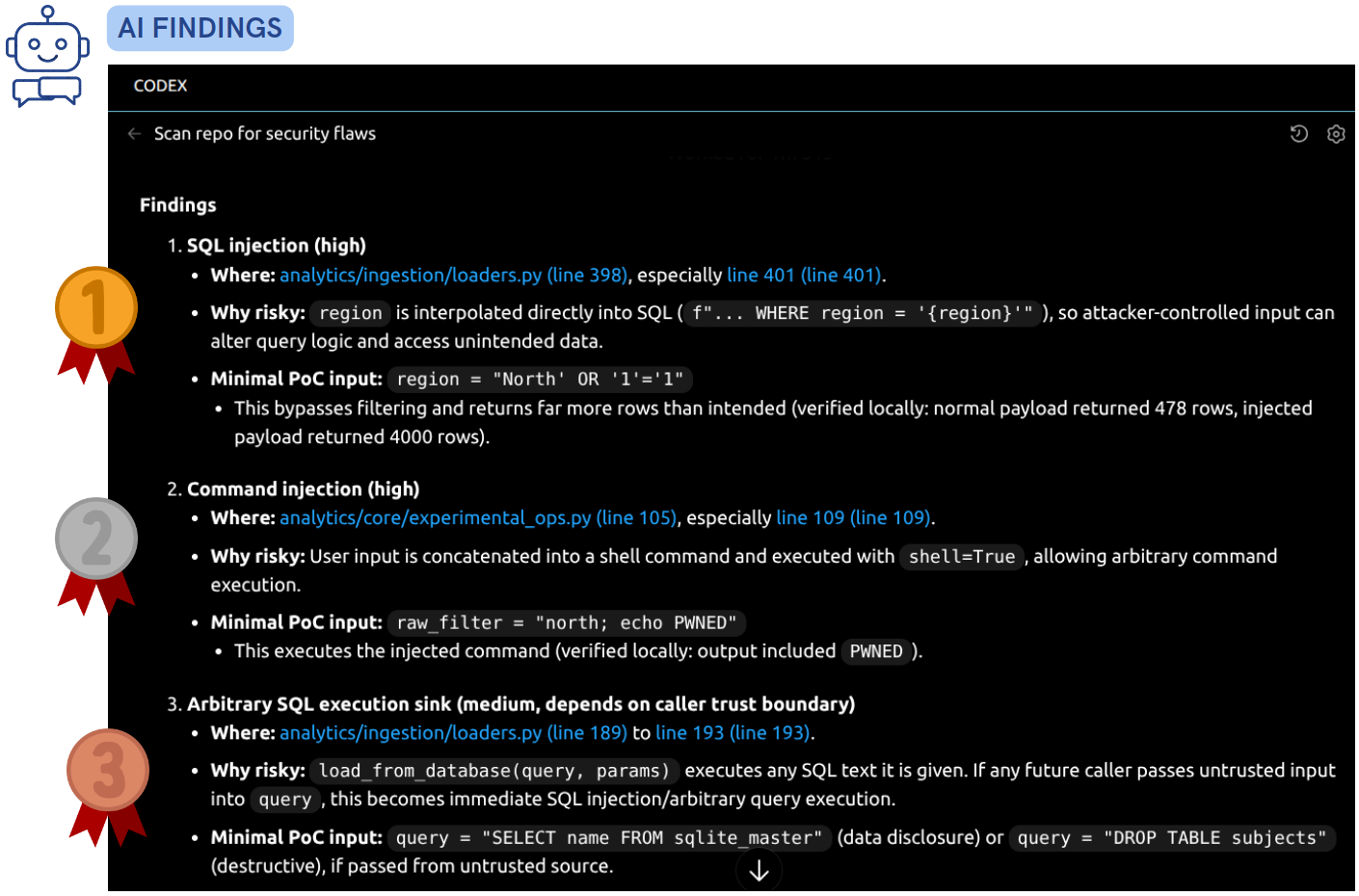
AI-assisted security review
🤖 Security prompt:
You are an application security engineer.
Scan this repository for common vulnerabilities such as SQL injection, cross-site scripting, cross-site request forgery, command injection, missing authentication and authorization checks, or sensitive data exposure. Follow the CWE Top 25 Most Dangerous Software Weaknesses.
For each finding include:
- Where it occurs and why it is risky.
- A minimal proof of concept input that could trigger it.
Security review output
Validating with security scanners
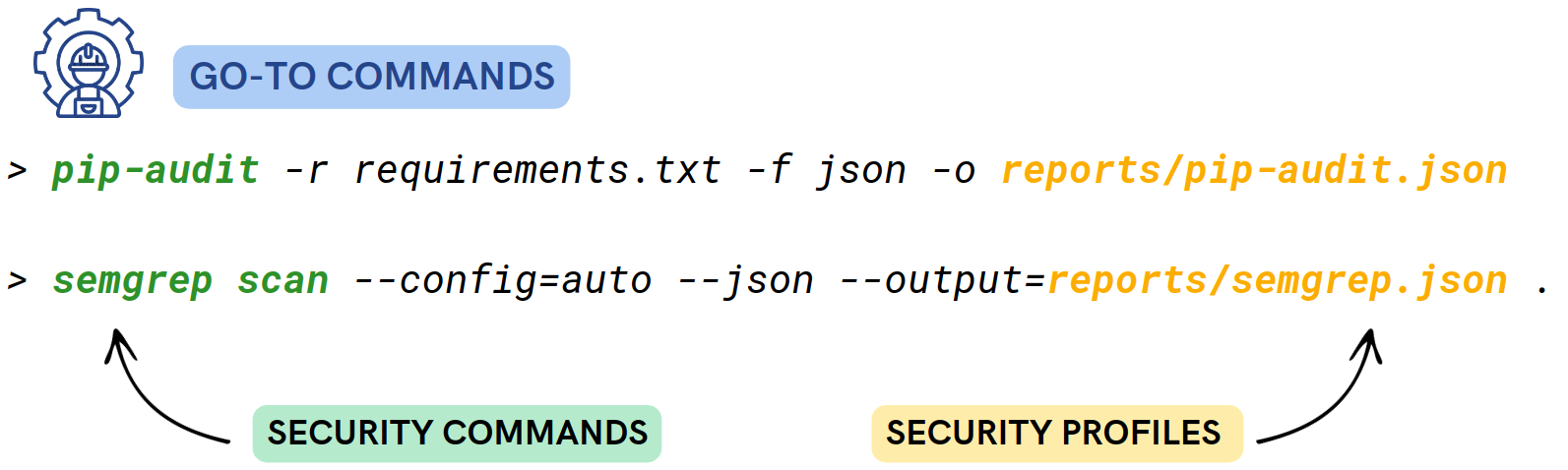
- Validate AI findings with scanners
pip-audit→ dependency vulnerabilitiessemgrep→ insecure code patterns
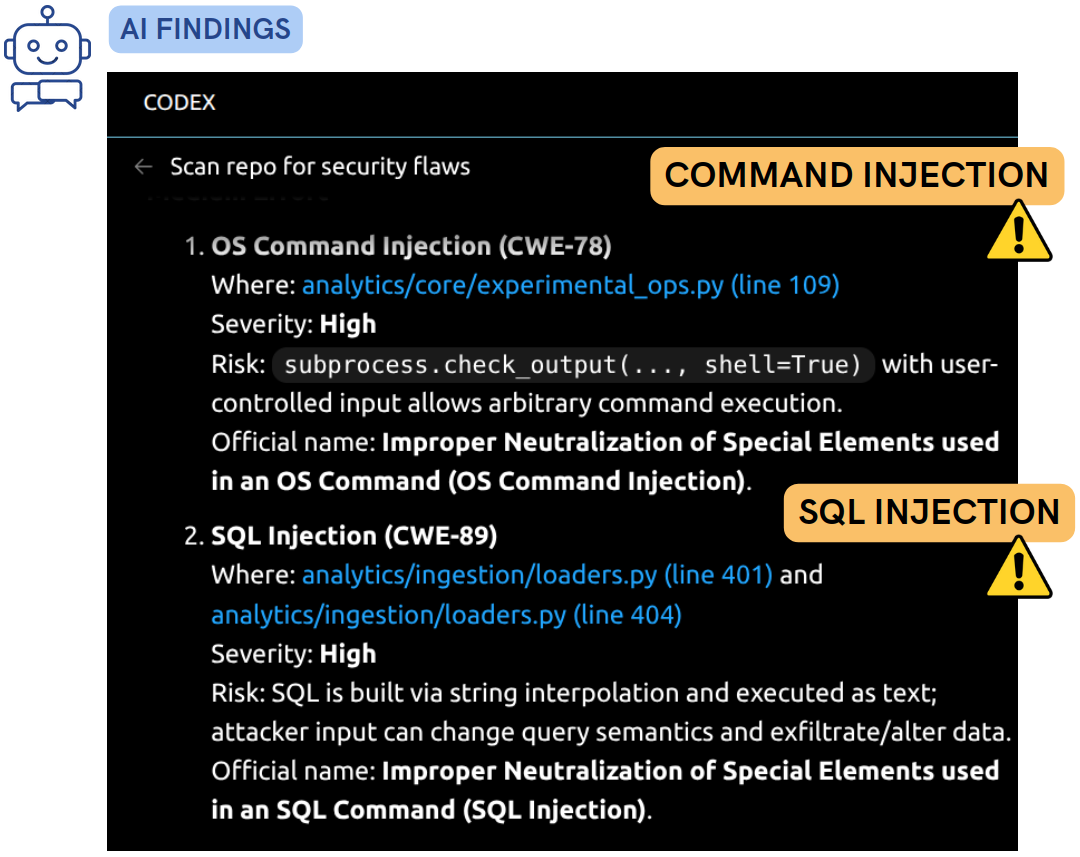
Interpreting scanner results
🤖 Interpreting results prompt:
Here are the scan outputs. Help me interpret the results and list the vulnerabilities found, using their official names when available.
Group the findings into quick fixes, medium effort, and architectural changes. For each finding, assess the risk and include its severity.
<copy security reports here>
Automating security checks
🤖 CI prompt:
Add the pip-audit and semgrep commands to this codebase's CI workflow to run regular security scans.
Configure the workflow to fail on high-severity findings and keep the output deterministic.
- Integrate into CI workflow
- Automate unit/integration tests
- Automate dependency auditing and static analysis
- Add OWASP ZAP for web services
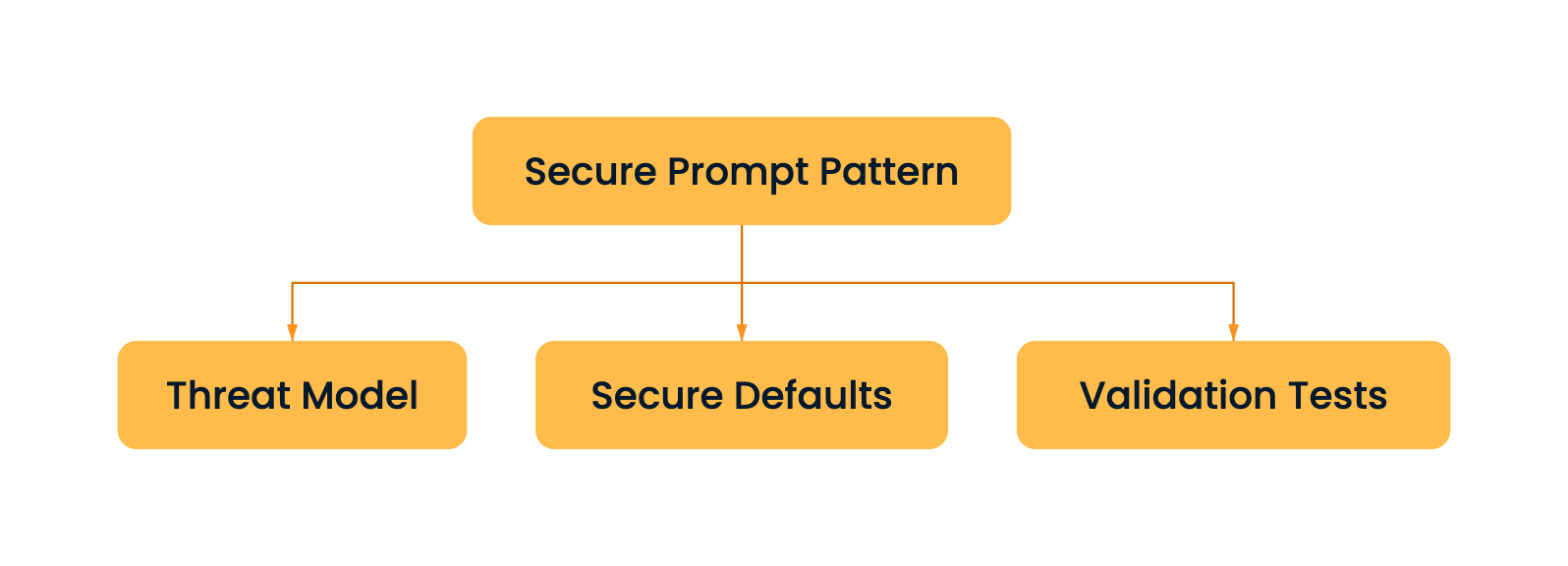
Secure prompt patterns

The three-part pattern
- Threat model → what needs protection
- Secure defaults → safer primitives
- Validation tests → prevent recurrence
Let's practice!
Advanced AI-Assisted Coding for Developers

